Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
OneLake security enables you to apply role-based access control (RBAC) to your data stored in OneLake. You can define security roles that grant access to specific folders within a Fabric item, then assign these roles to users or groups. Roles can also contain row or column level security to further limit access. The OneLake security permissions determine what data that user can see across all experiences in Fabric.
Fabric users with Write and Reshare permissions (generally Admin and Member workspace users) can get started by creating OneLake security roles to grant access to only specific folders or tables in a Fabric data item. To grant access to data in an item, add users to a data access role. Users that aren't part of a data access role see no data in that item.
What types of data can be secured?
Use OneLake security roles to manage OneLake read access to any tables or folders in a supported data item. Access to tables can be further restricted using row and/or column level security. Any security set applies to access from all engines in Fabric. For more information, see the data access control model.
For specific item types, you can also configure ReadWrite access. This permission gives users the ability to edit data in a lakehouse on specified tables or folders without giving them access to create or manage Fabric items. ReadWrite access enables users to perform write operations through Spark notebooks, the OneLake file explorer, or OneLake APIs. Write operations through the Lakehouse UX for viewers isn't supported.
The following data items support OneLake security:
| Fabric item | Supported permissions |
|---|---|
| Lakehouse | Read, ReadWrite |
| Azure Databricks Mirrored Catalog | Read |
| Mirrored Databases | Read |
Default settings
When you create a new item, it comes with a set of default roles. Default roles ensure that privileged users can see and interact with data in the newly created item. Different items have different default roles depending on that item's use cases, but most contain a DefaultReader role. By using virtualized role memberships, all users that have the necessary permissions to view data in the item (the ReadAll permission, for example) are included as members of this default role. To restrict access to those users, delete the DefaultReader role or remove the ReadAll permission from the accessing users.
Newly created items that have a corresponding SQL analytics endpoint start in User's identity mode by default. Admins and Members can change the mode at any time in the Endpoint's settings.
Important
When you add a user to a data access role, make sure that you remove them from the DefaultReader role. Otherwise, they maintain full access to the data.
Enable OneLake security for SQL analytics endpoint
Before you can use OneLake security with SQL analytics endpoint, you must configure it to use User's identity access mode.
Note
You only need to switch to User's identity access mode once per SQL analytics endpoint. Endpoints that aren't switched to user's identity mode continue to use a delegated identity to evaluate permissions.
Go to SQL analytics endpoint.
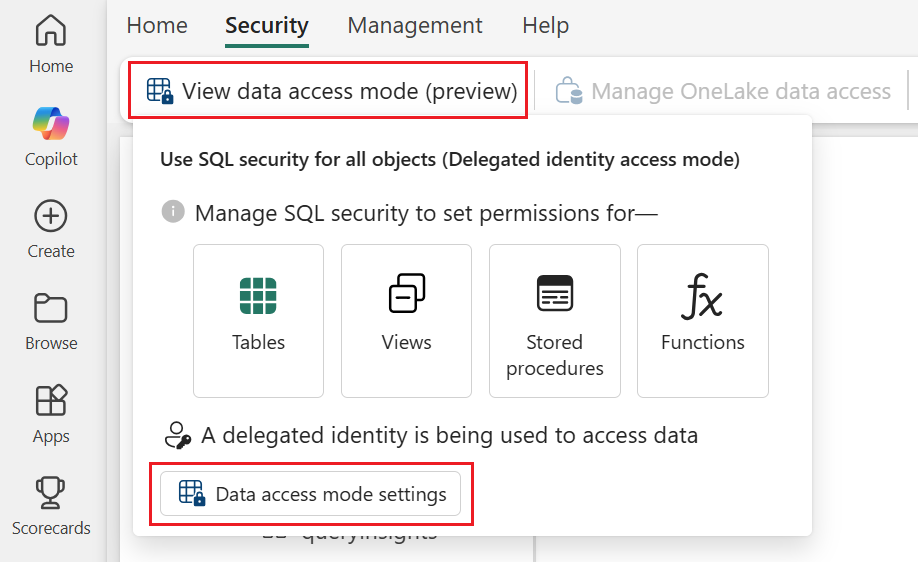
In the SQL analytics endpoint experience, select the Security tab.
Select View data access mode (preview) > Data access mode settings.
Select Use OneLake security for tables (User's identity access mode), then select Apply.
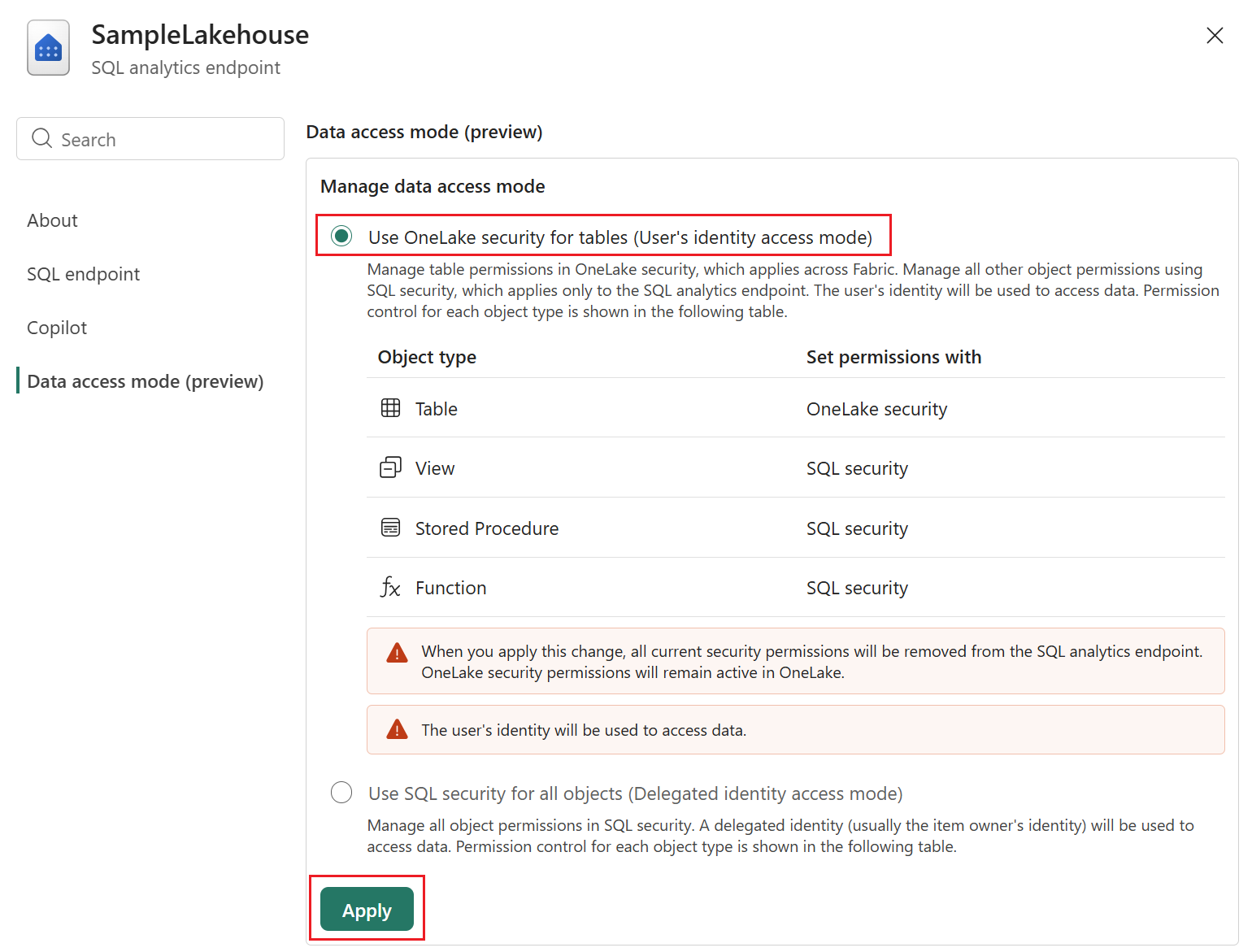
Select Continue to confirm your choice.
Now the SQL analytics endpoint is ready to use with OneLake security.